How to Configure Glitter AI SSO with Microsoft Entra ID
Learn how to set up Microsoft Entra ID as your SAML Identity Provider to manage Single Sign-On (SSO) authentication for Glitter AI.
This guide demonstrates how to configure Microsoft Entra ID as a SAML Identity Provider (IdP) to enable Single Sign-On (SSO) for your Glitter AI organization. Configuring SSO streamlines application access and centralizes authentication management.
This workflow applies to IT administrators and workspace owners responsible for identity management. You will need admin privileges in both Microsoft Entra ID and Glitter AI to complete this setup.
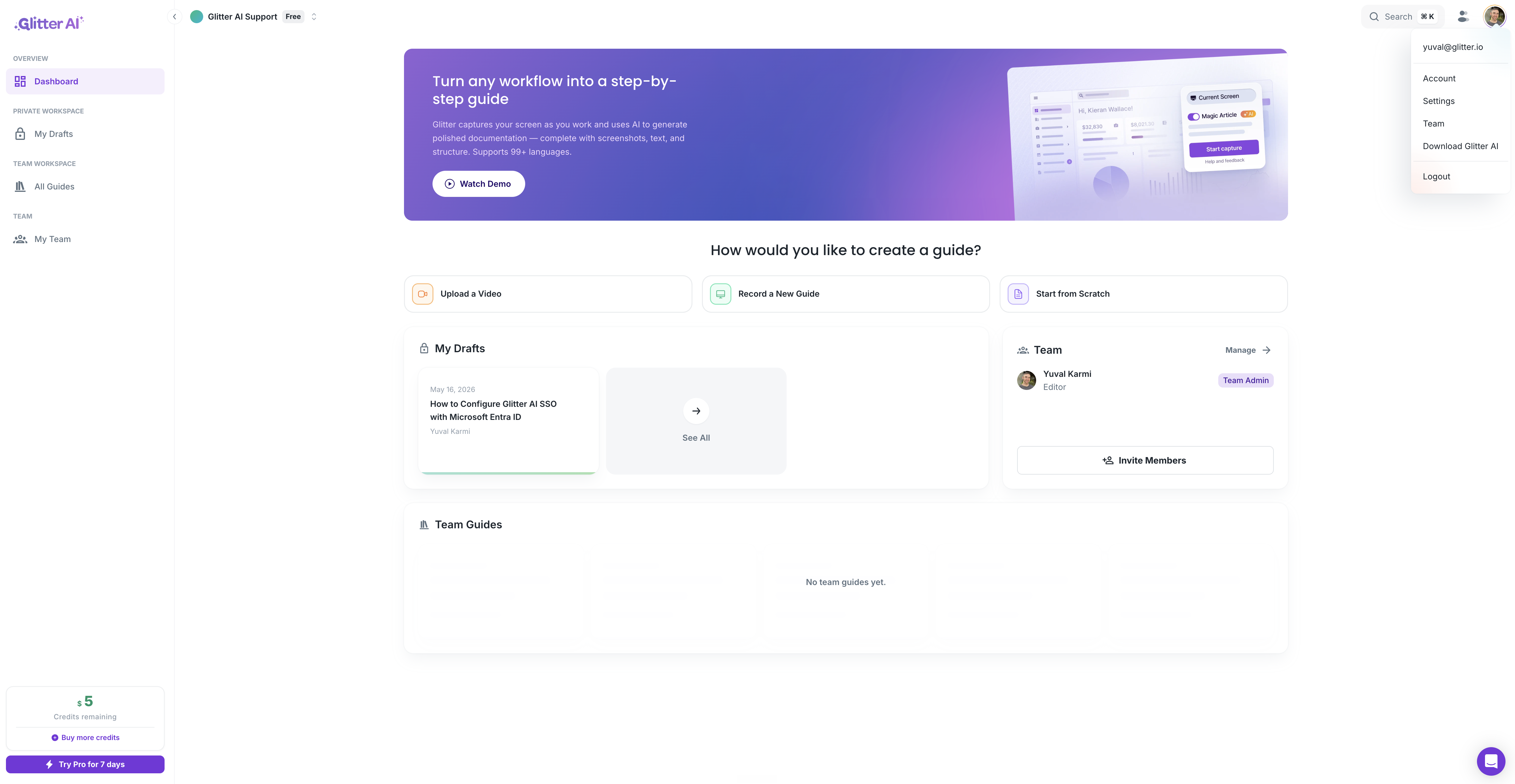
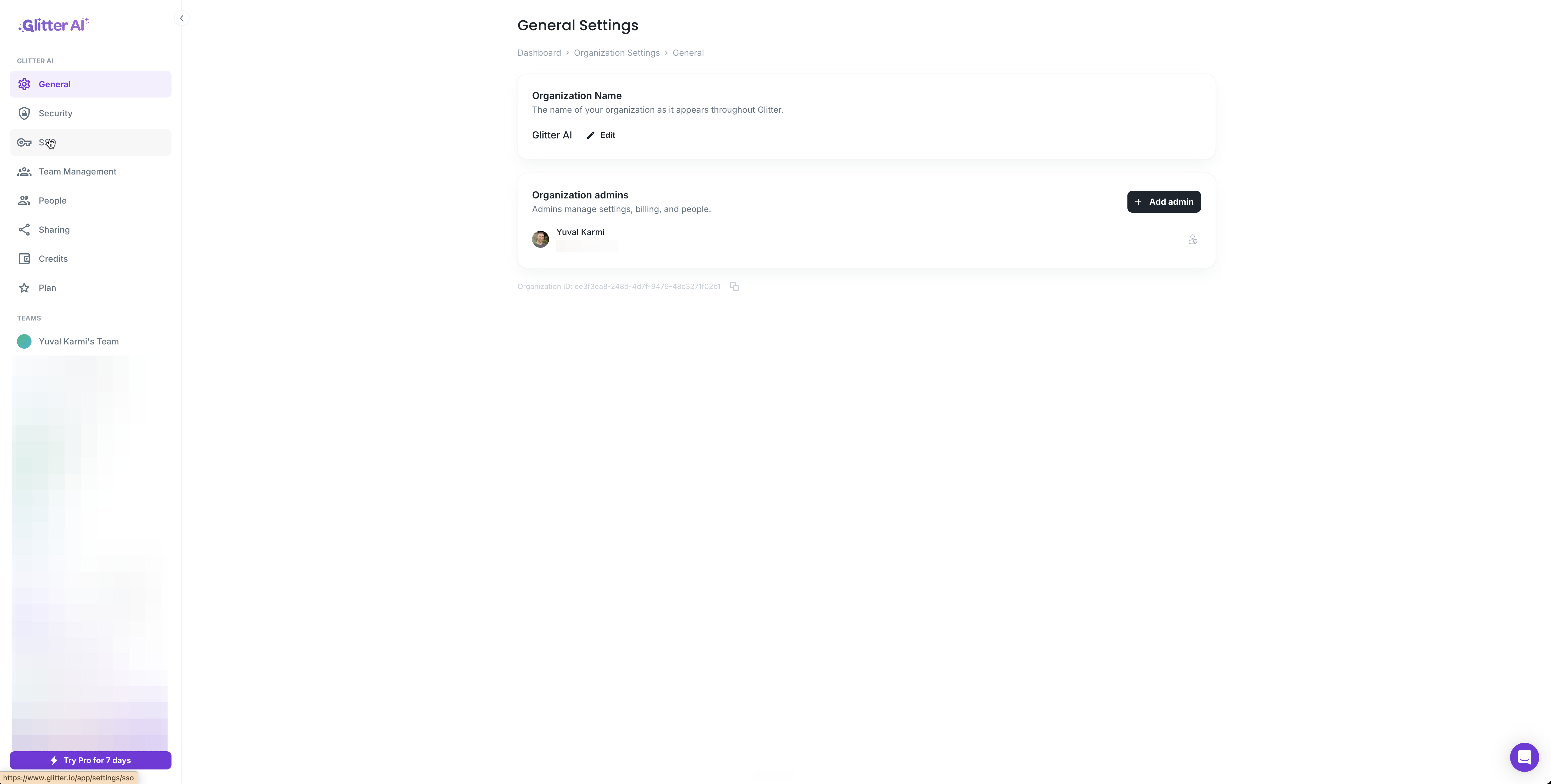
Retrieve Glitter AI SSO Details
To begin, you need to collect your organization's unique SAML parameters from the Glitter AI application.
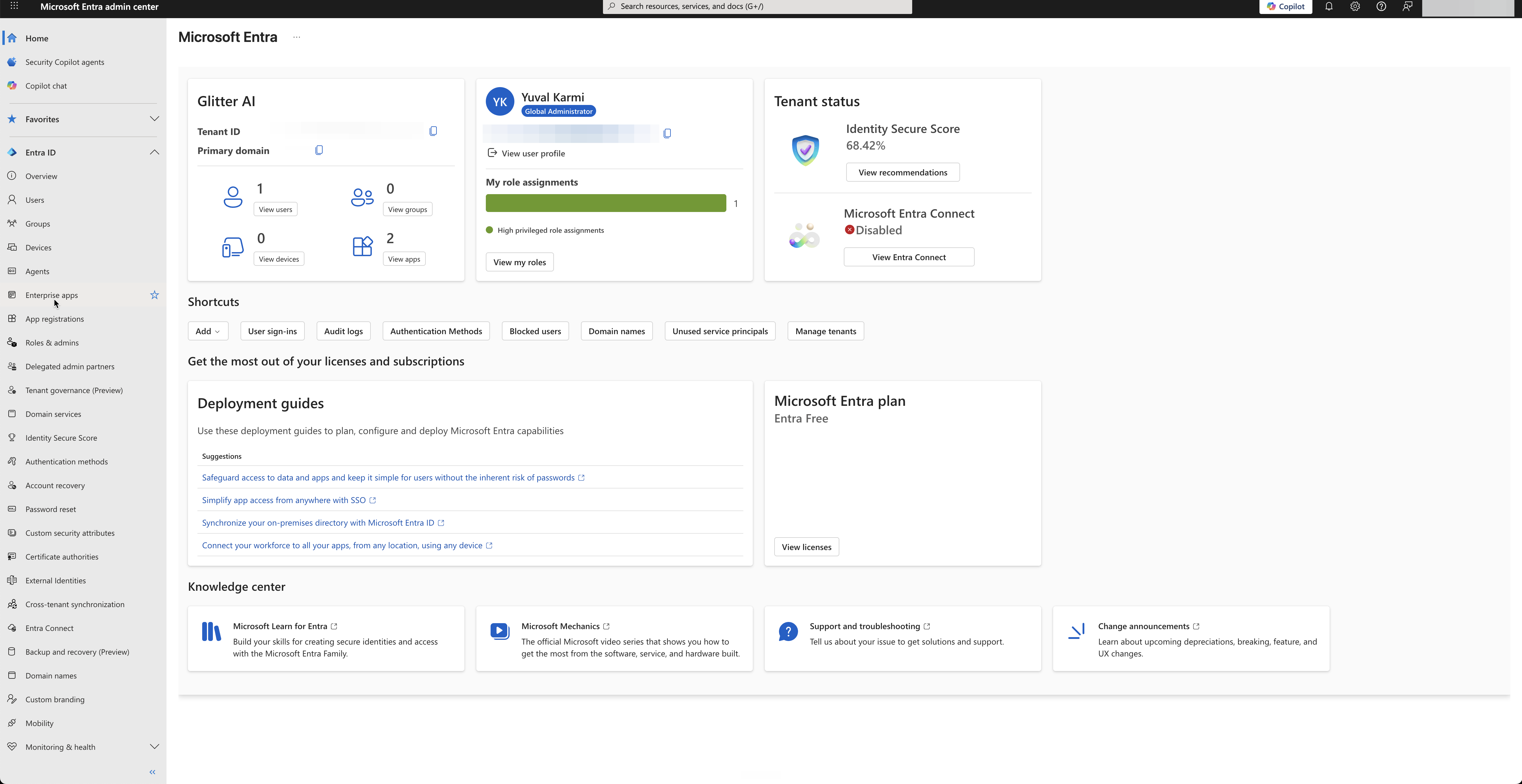
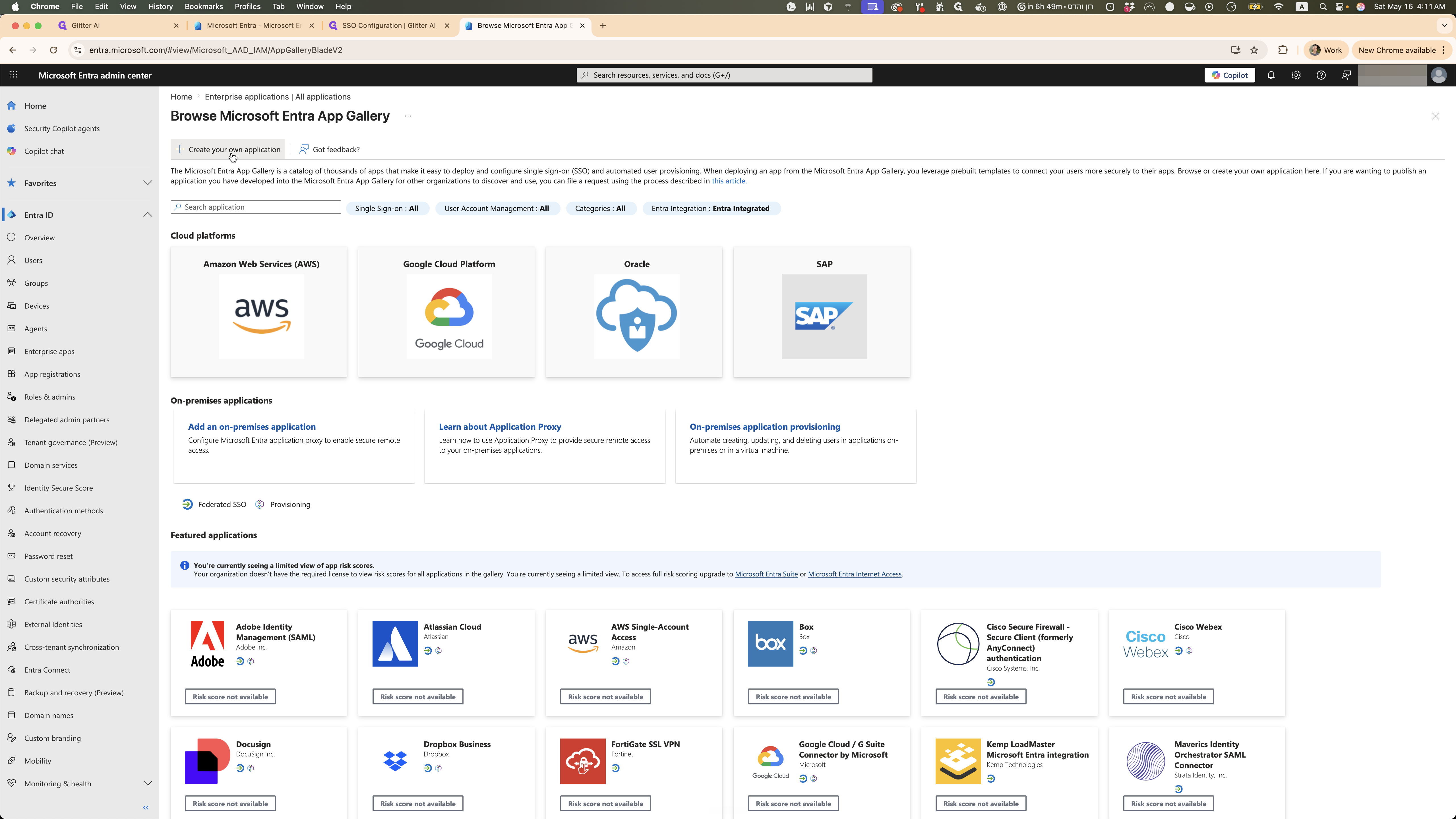
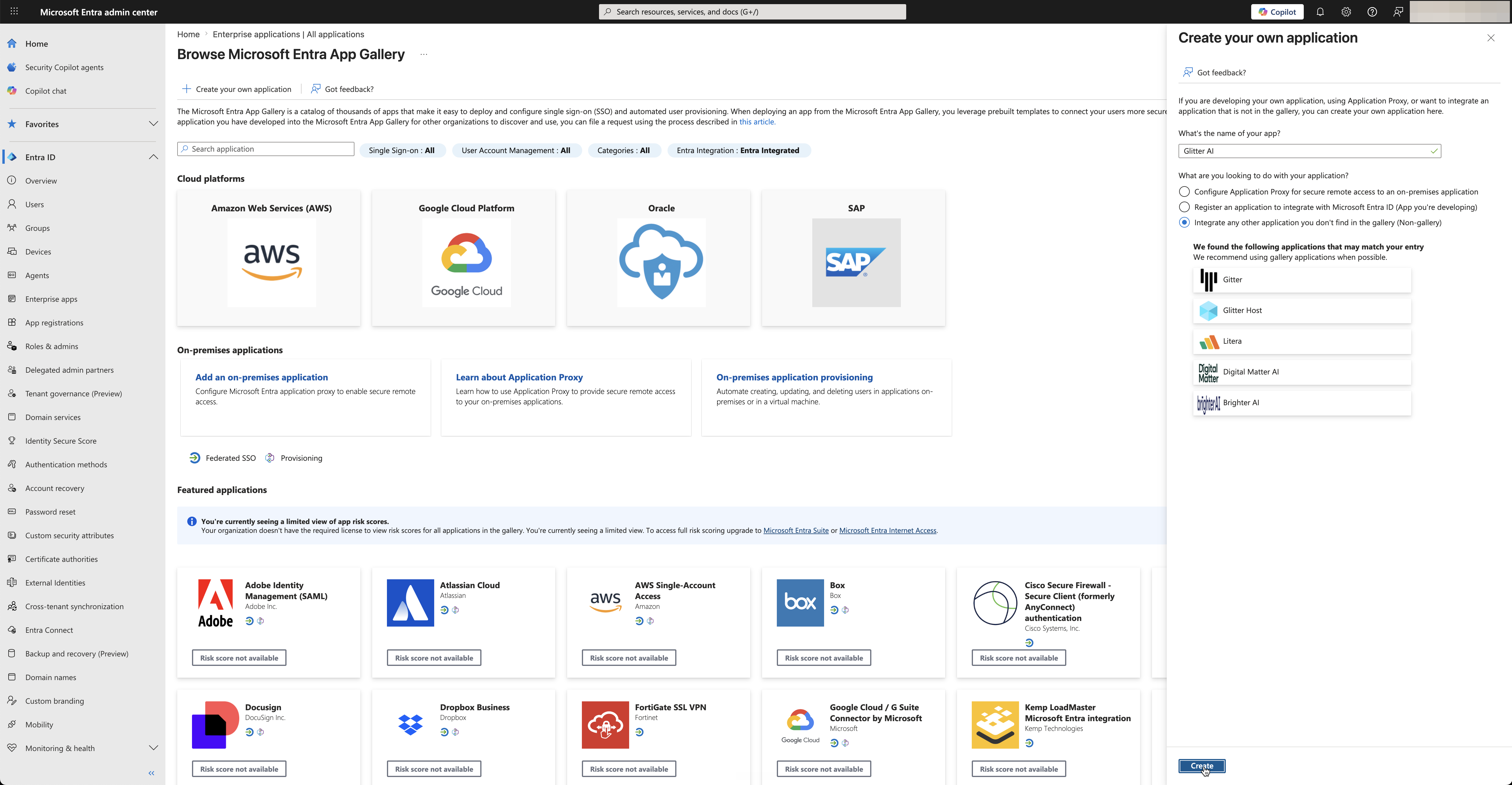
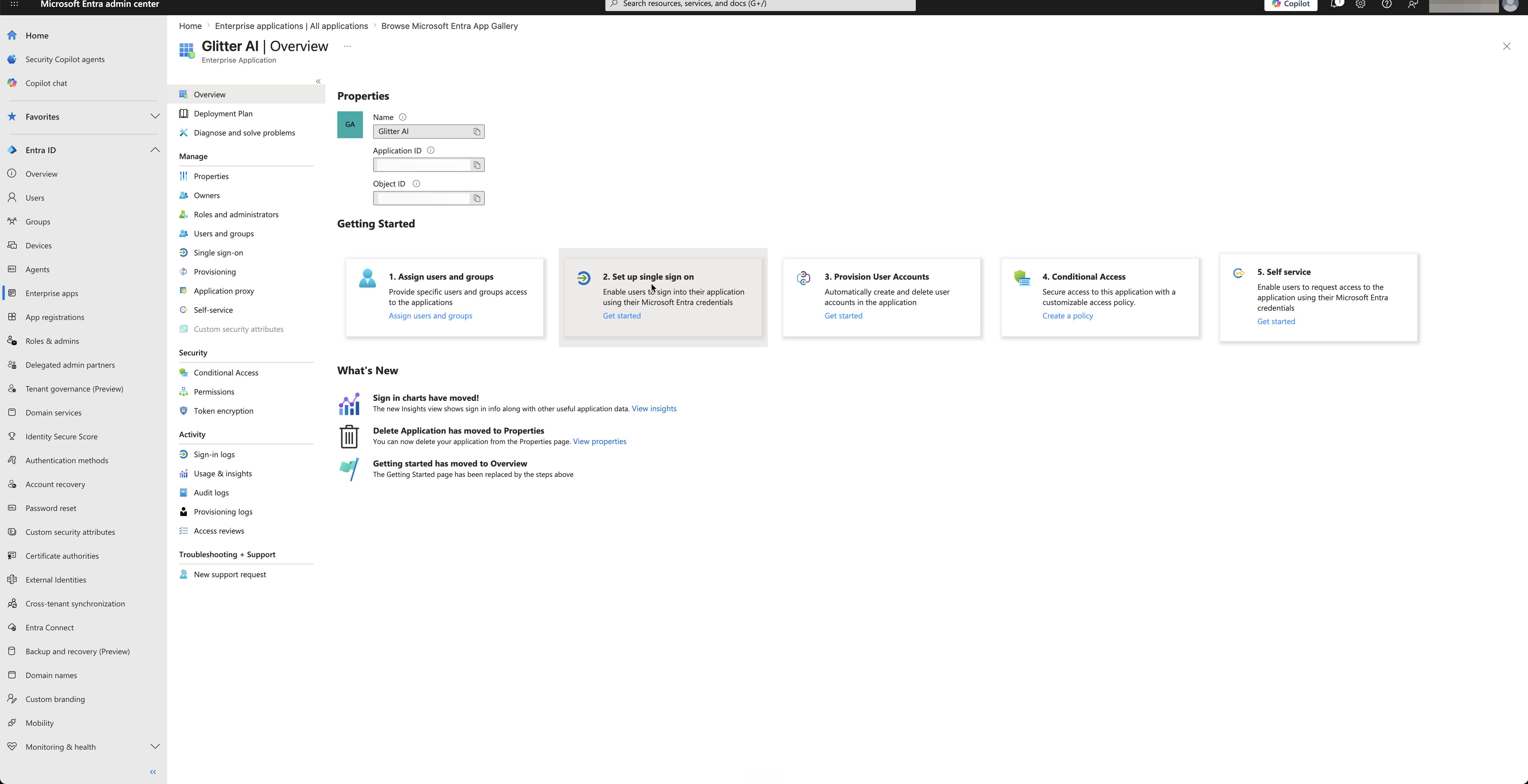
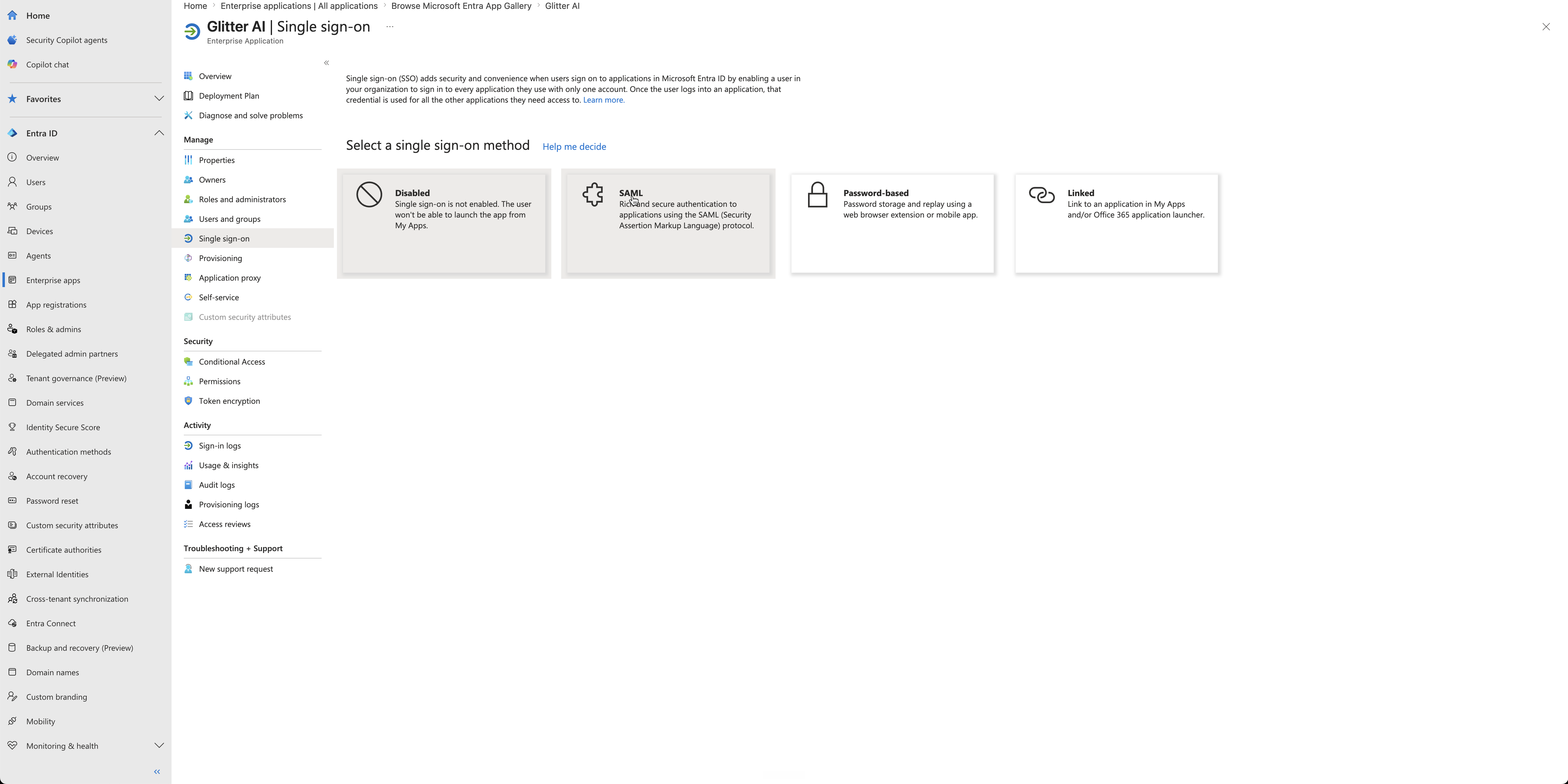
Create the Entra ID Enterprise Application
Log in to the Microsoft Entra admin center to register Glitter AI as a new application.
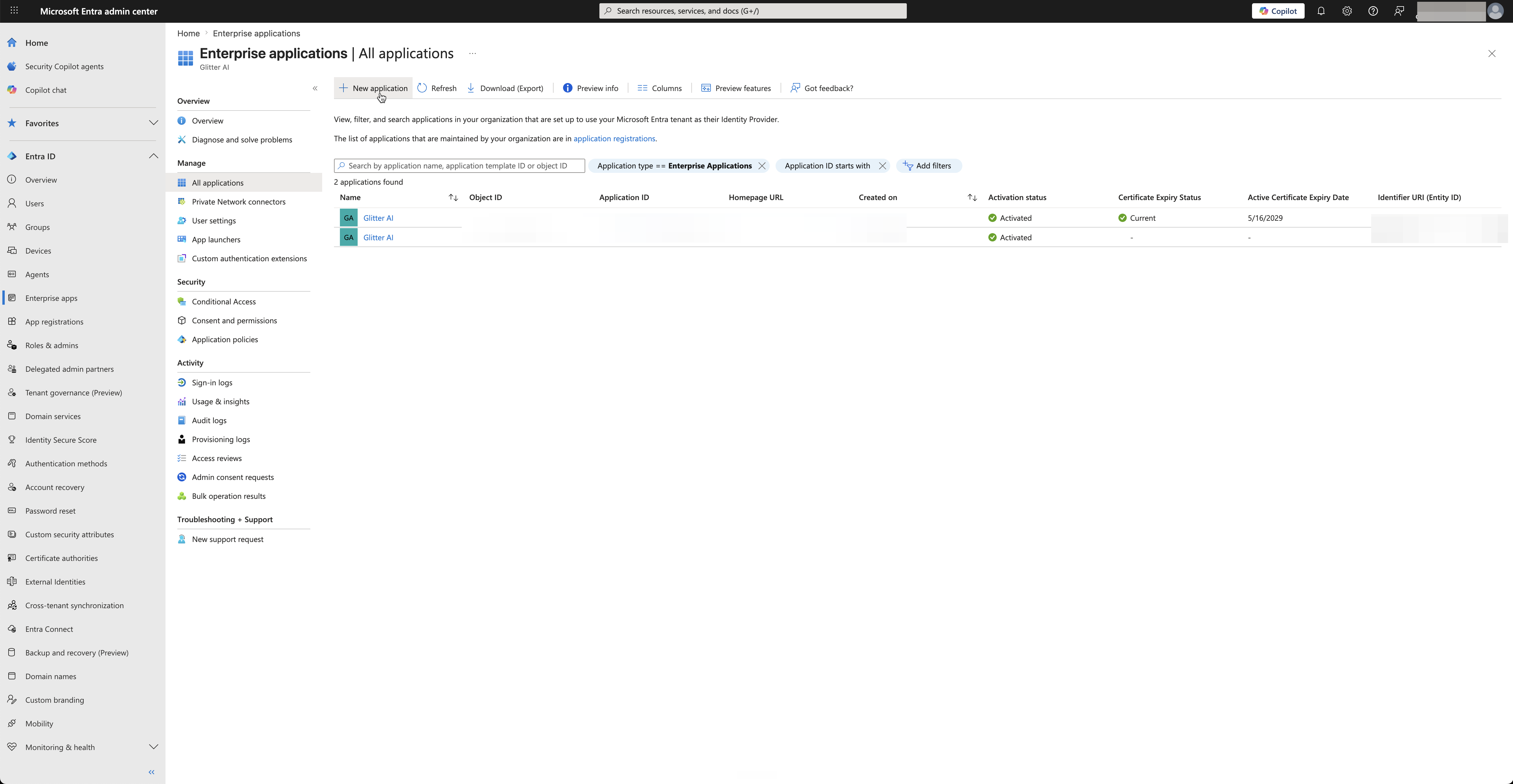
Glitter AI.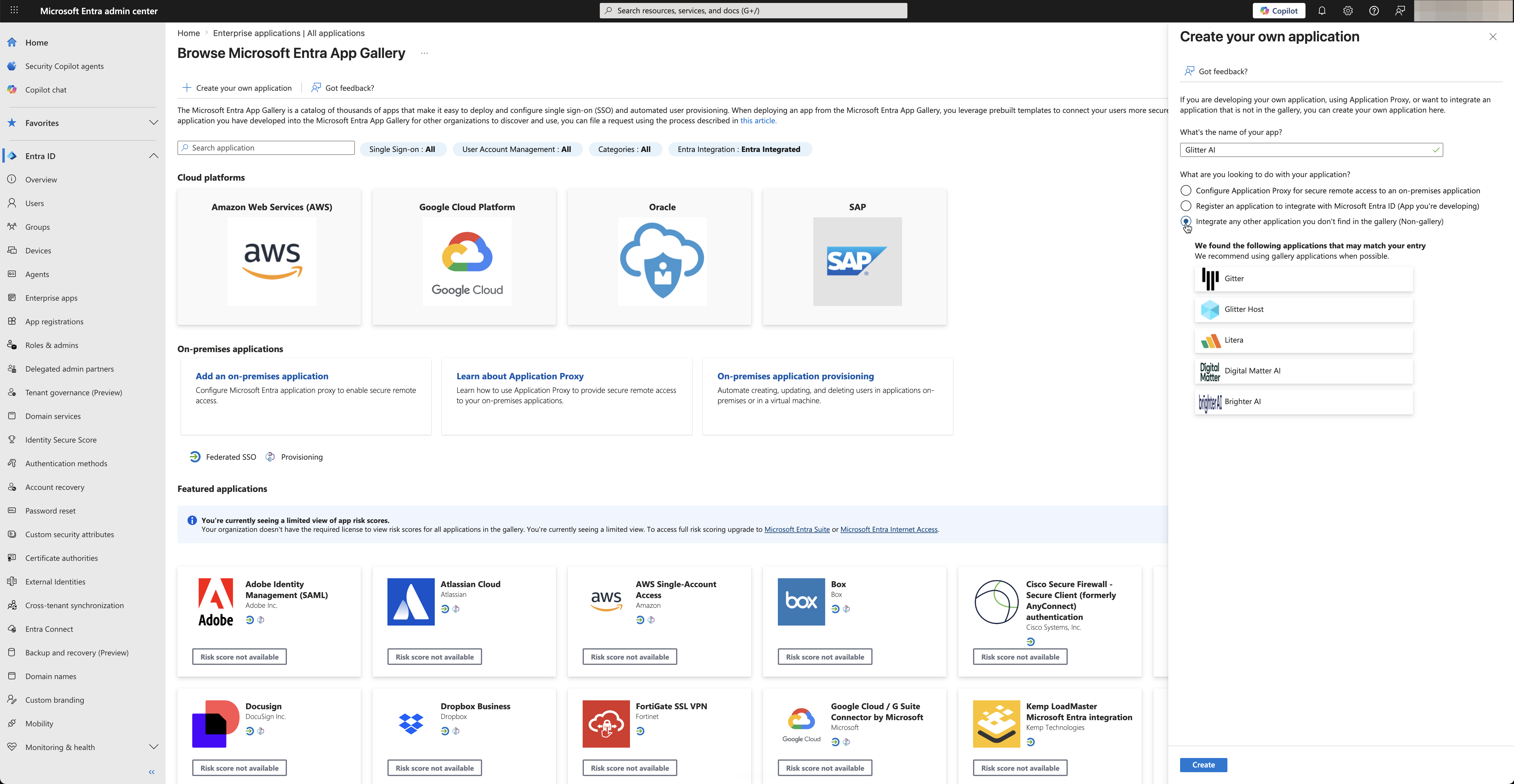
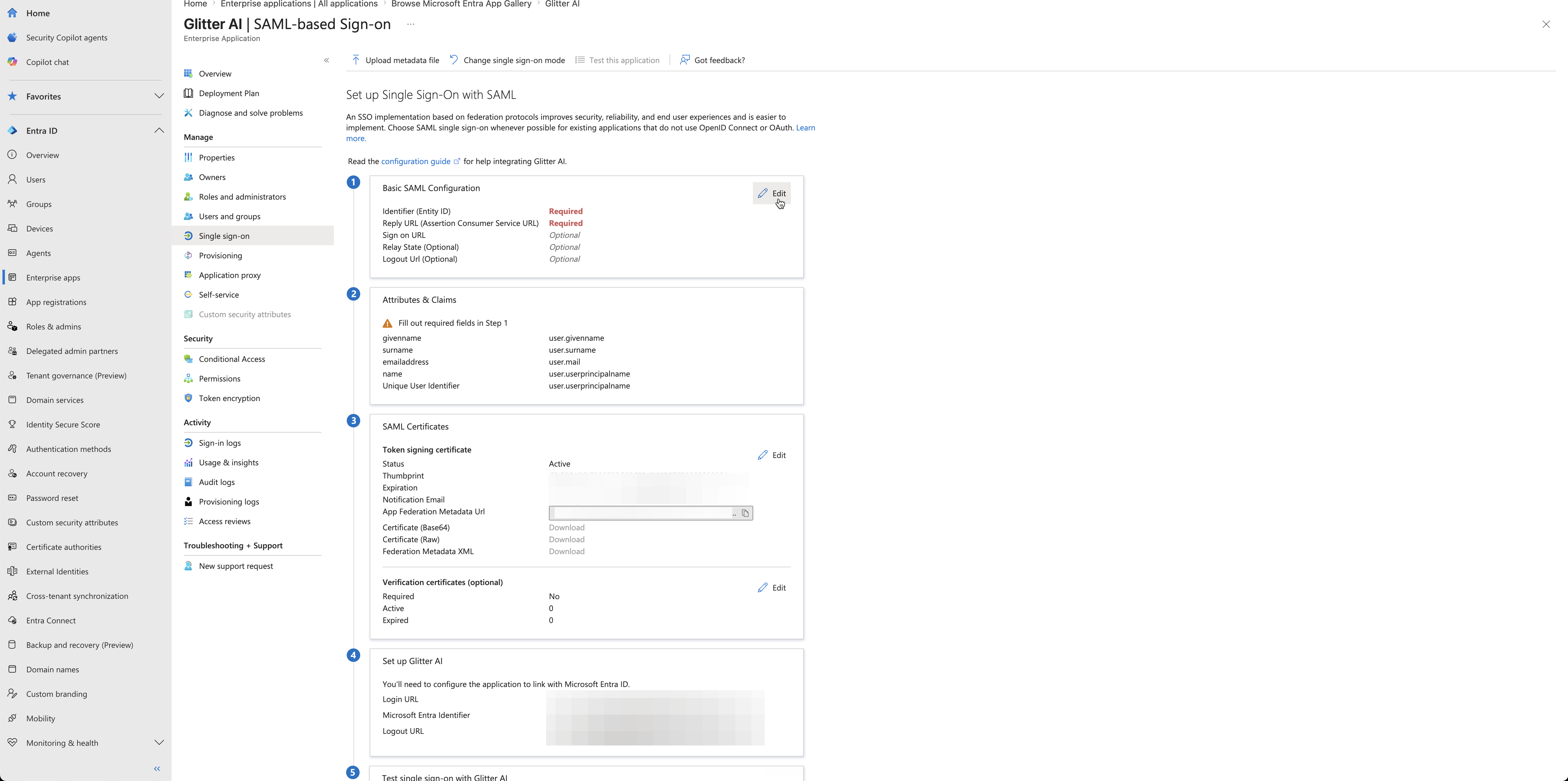
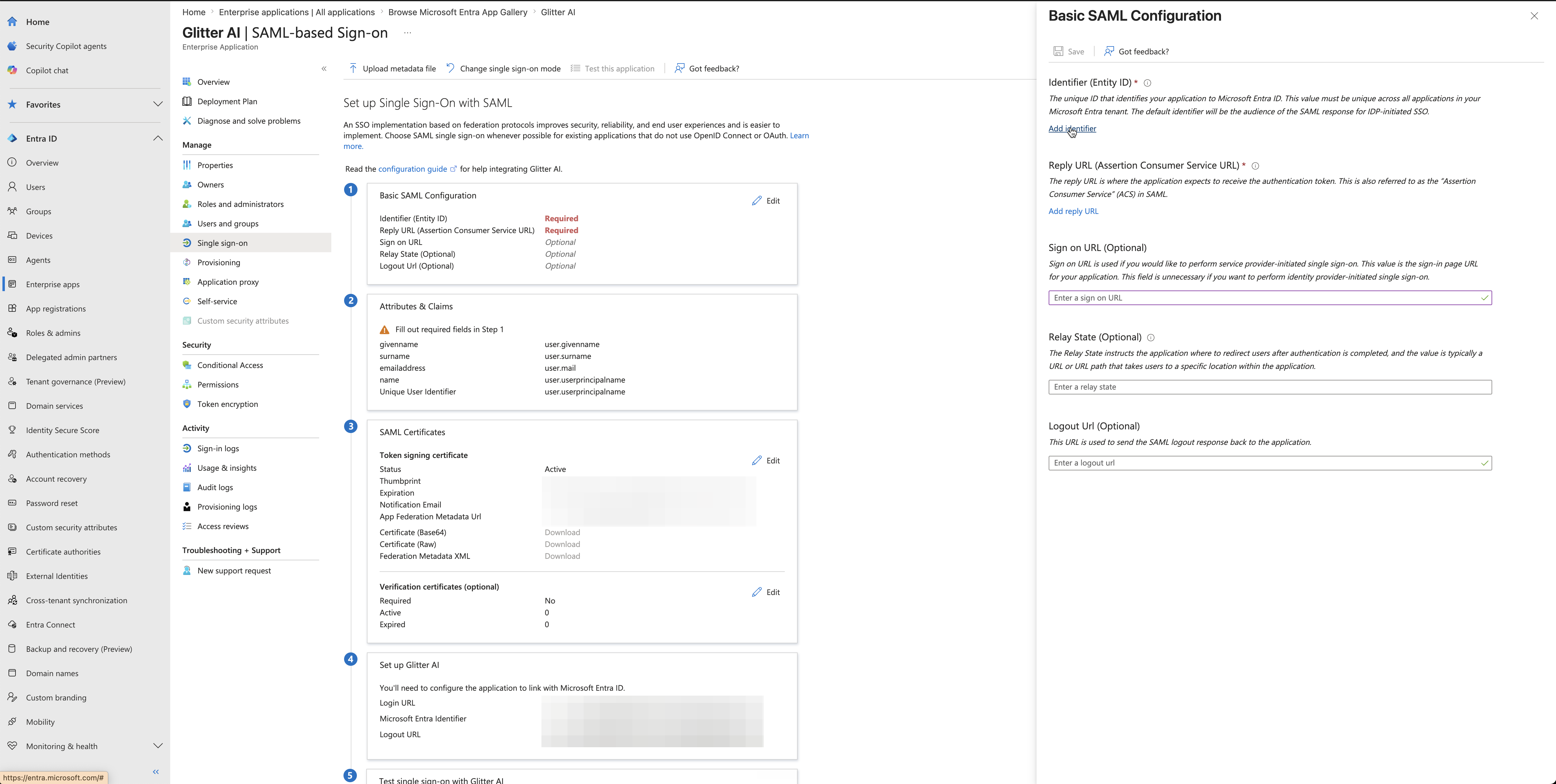
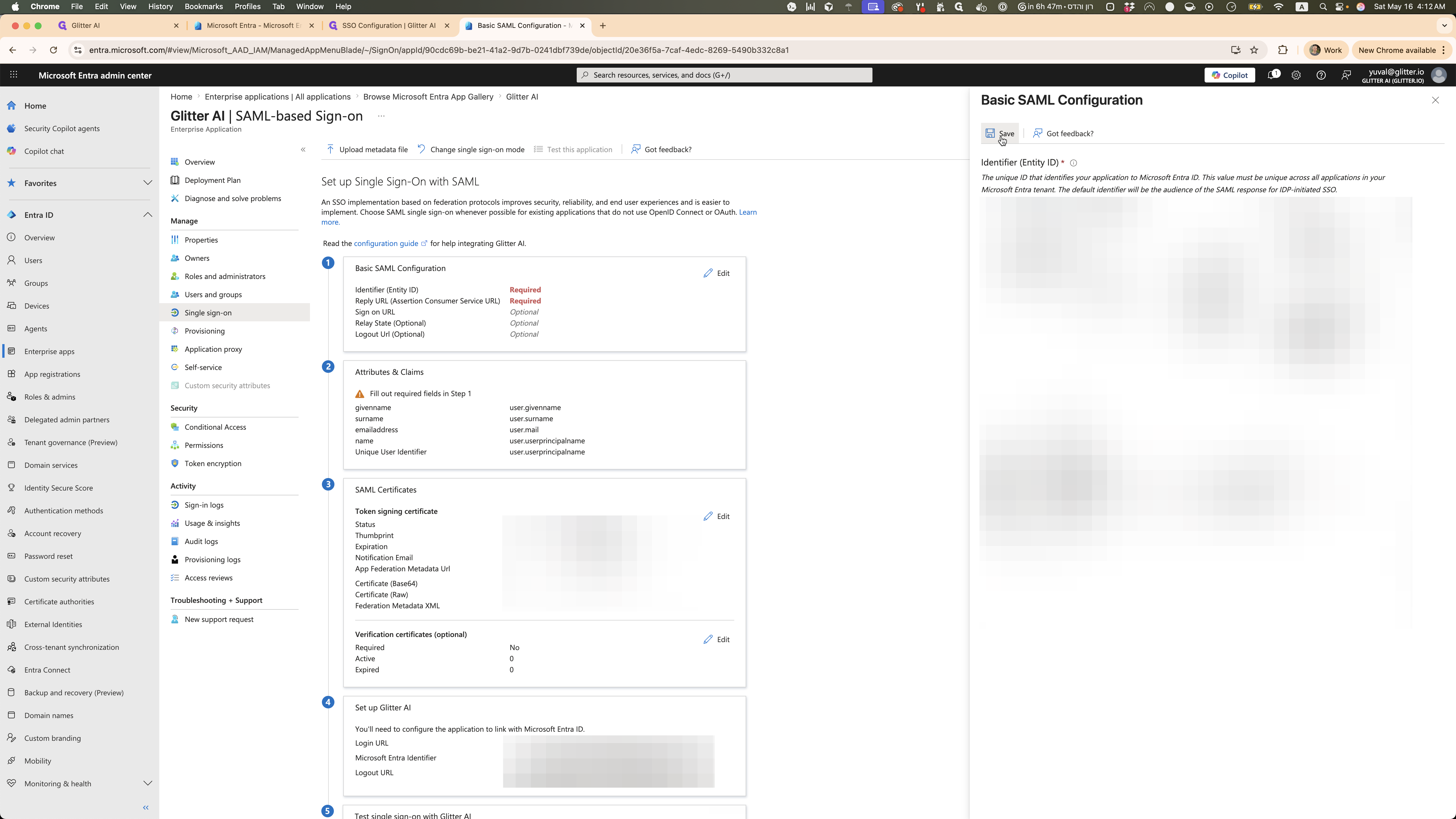
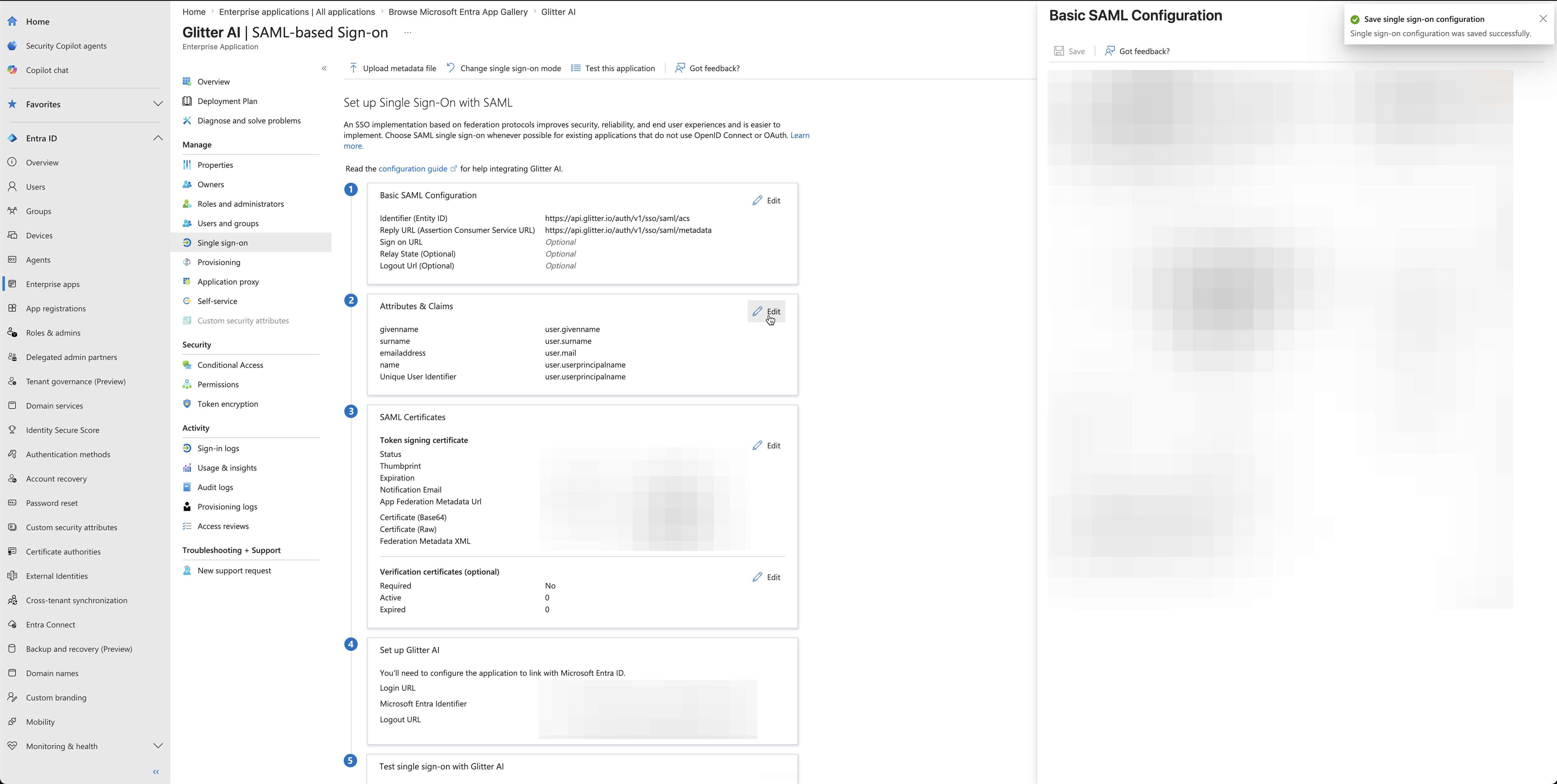
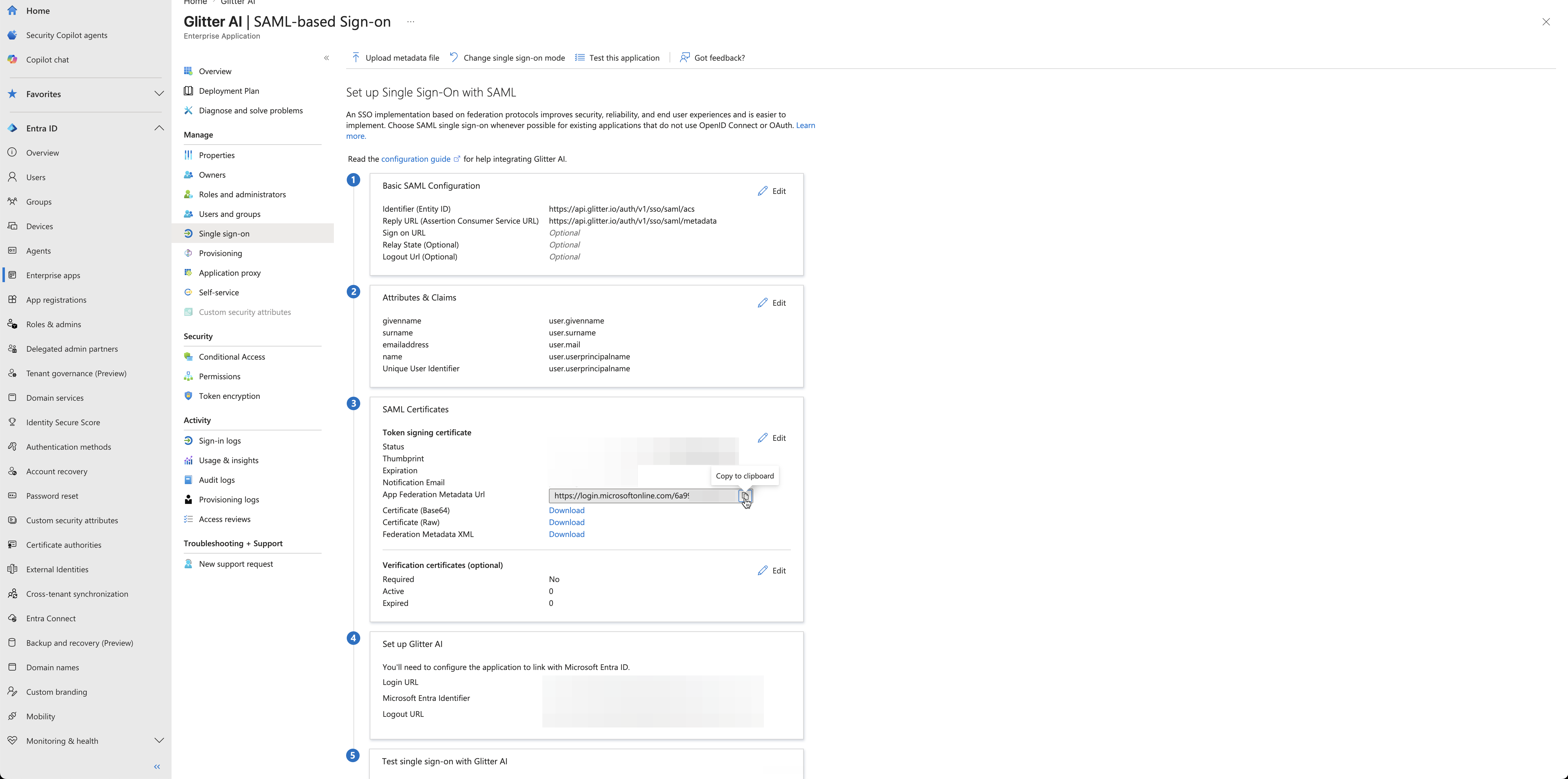
Configure SAML Settings in Entra ID
Now you will link Entra ID to Glitter AI using the Service Provider details you located earlier. Reference the mapping table below to ensure you paste the correct URLs into Entra ID.
Entra ID Field | Glitter AI Value to Paste |
|---|---|
Identifier (Entity ID) | Entity ID (Audience URI) |
Reply URL (Assertion Consumer Service URL) | ACS URL |
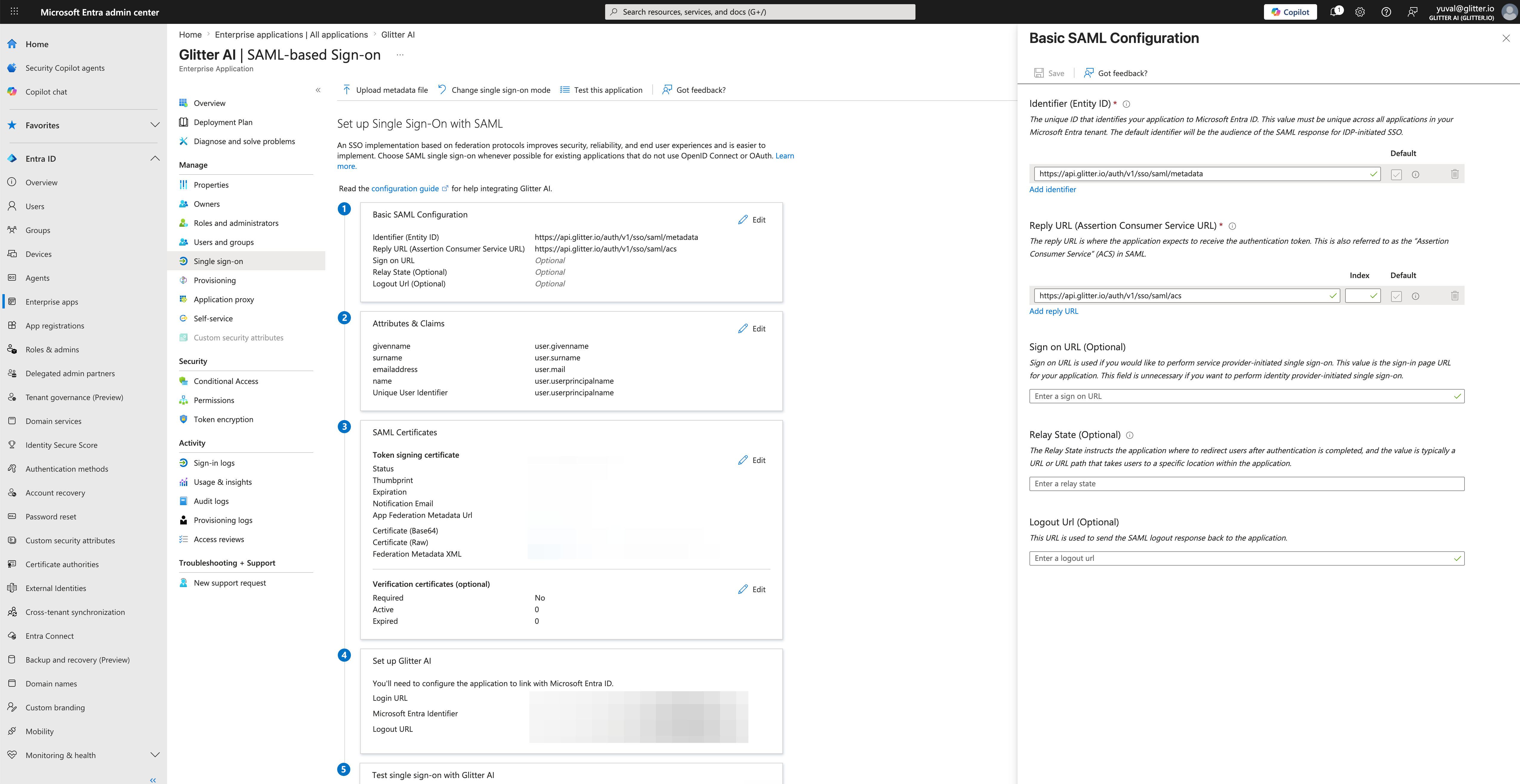
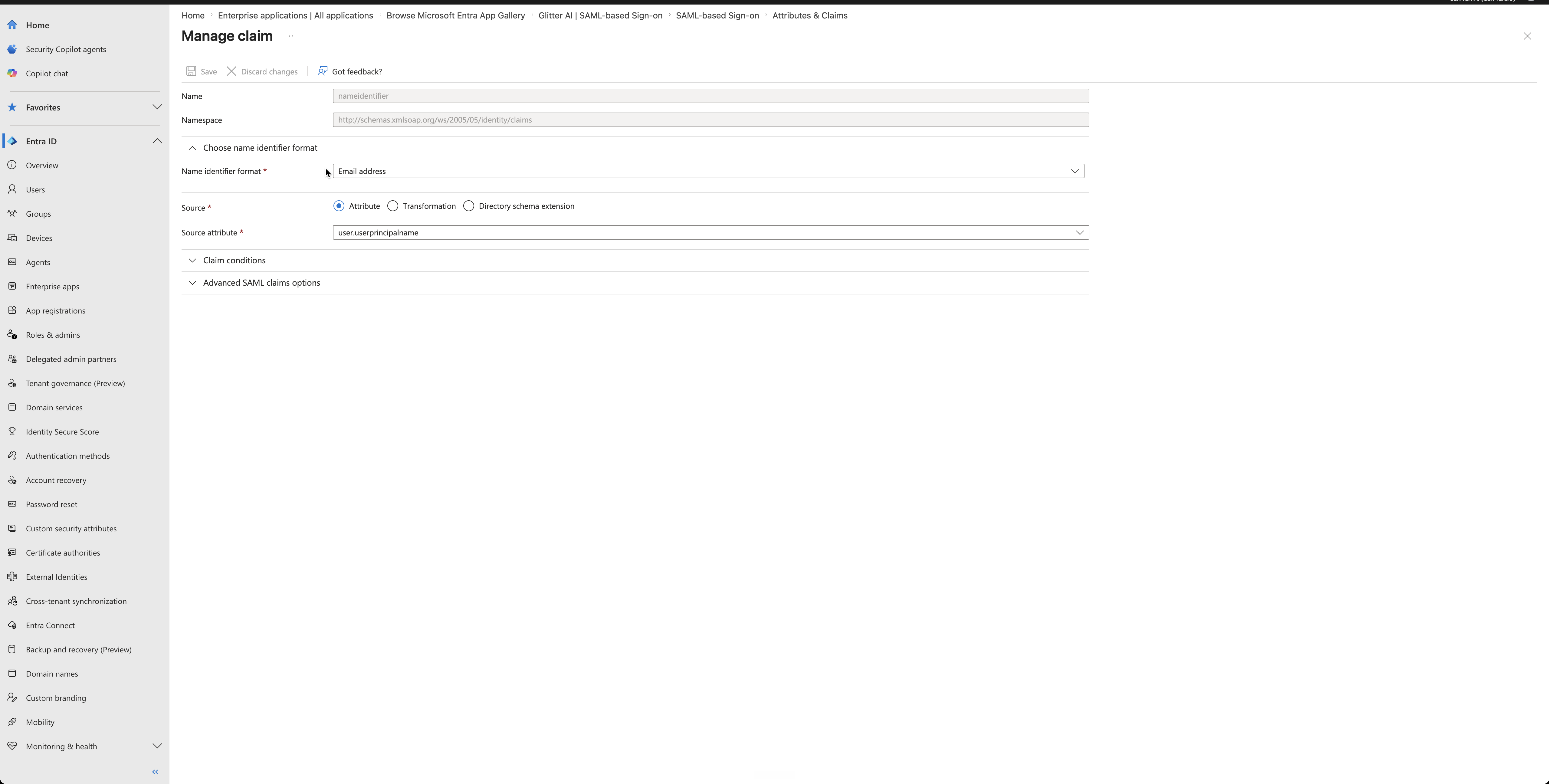
Verify Attributes and Claims
Glitter AI requires users to pass an email address format to authenticate correctly.
user.userprincipalname.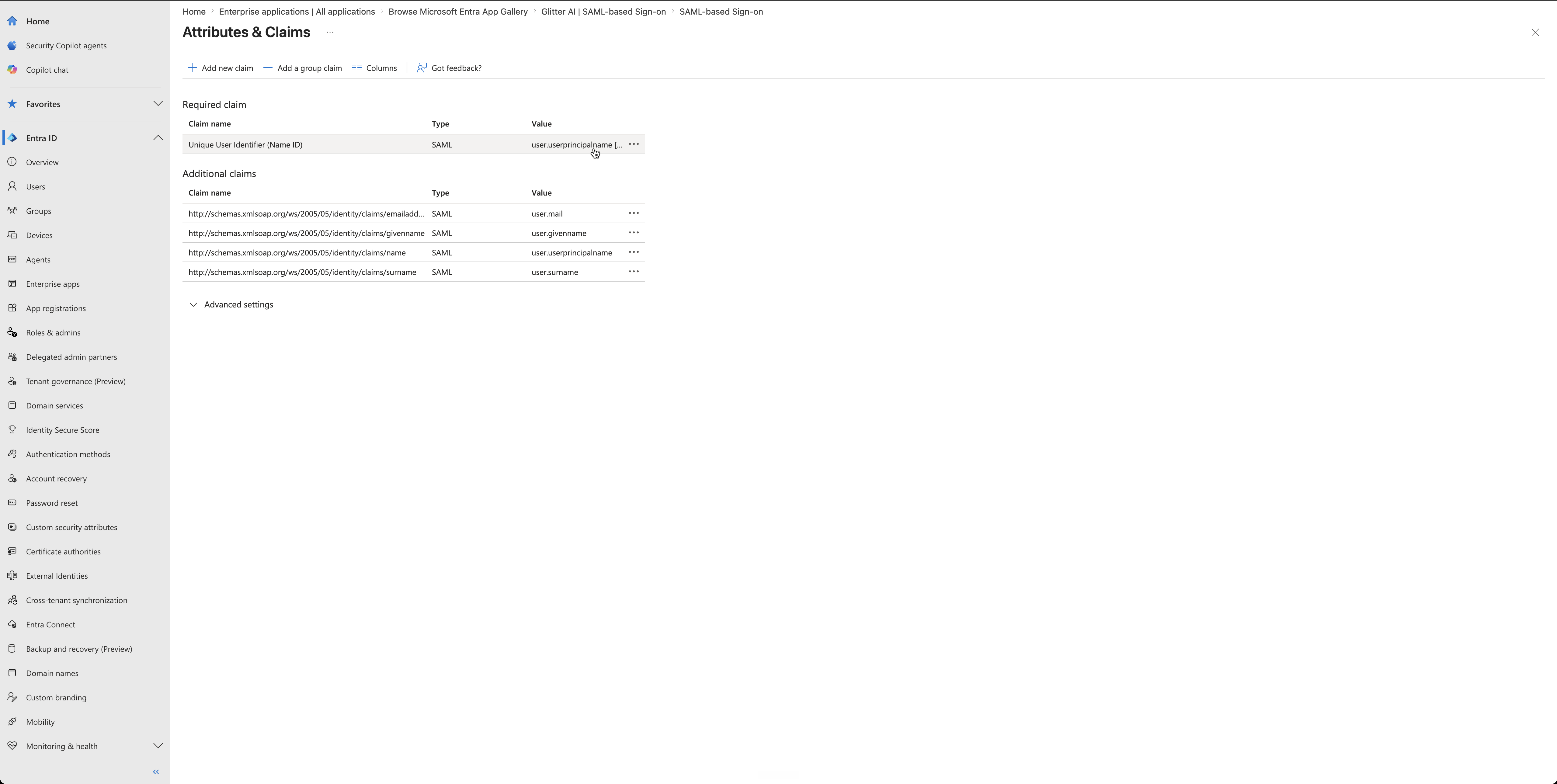
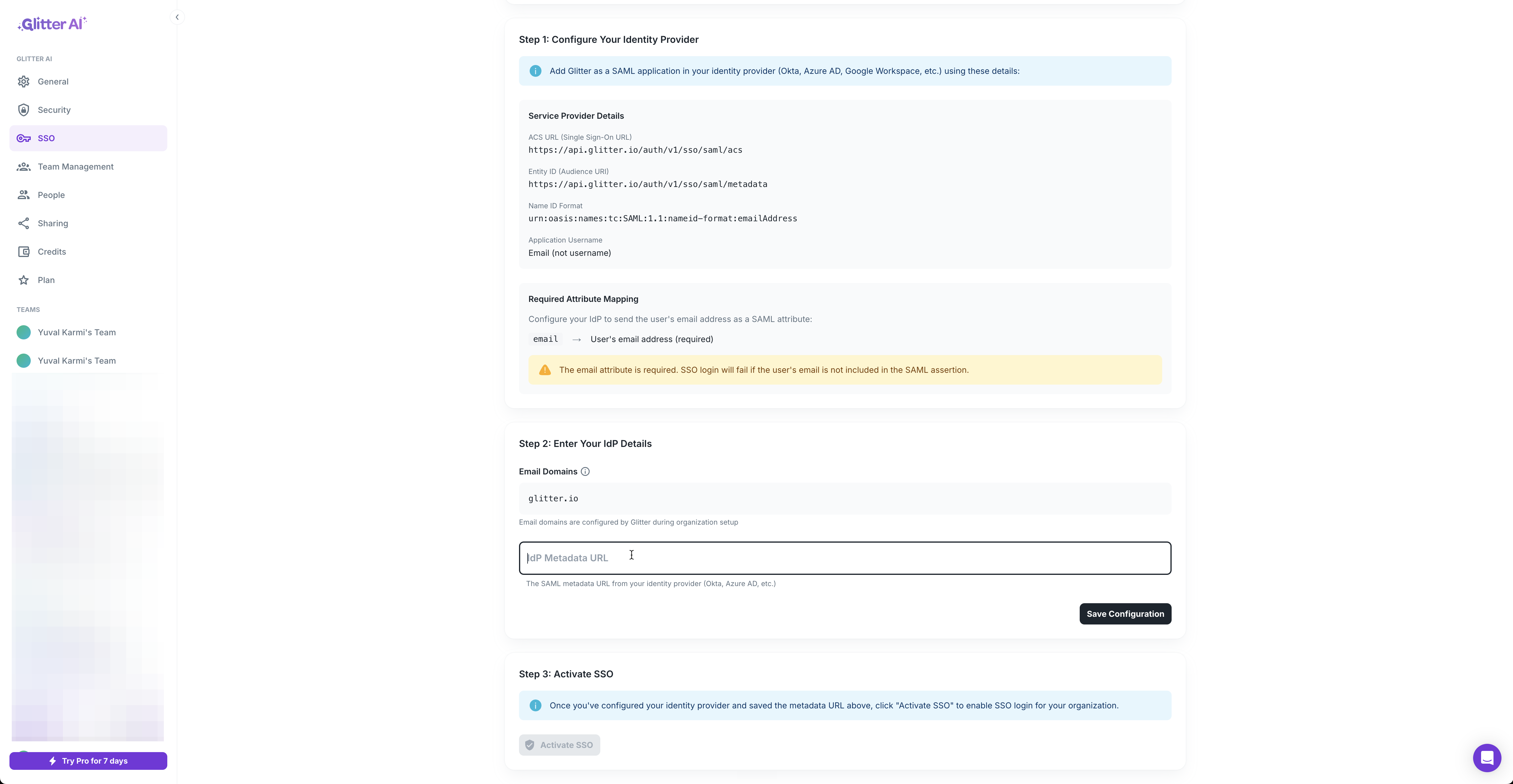
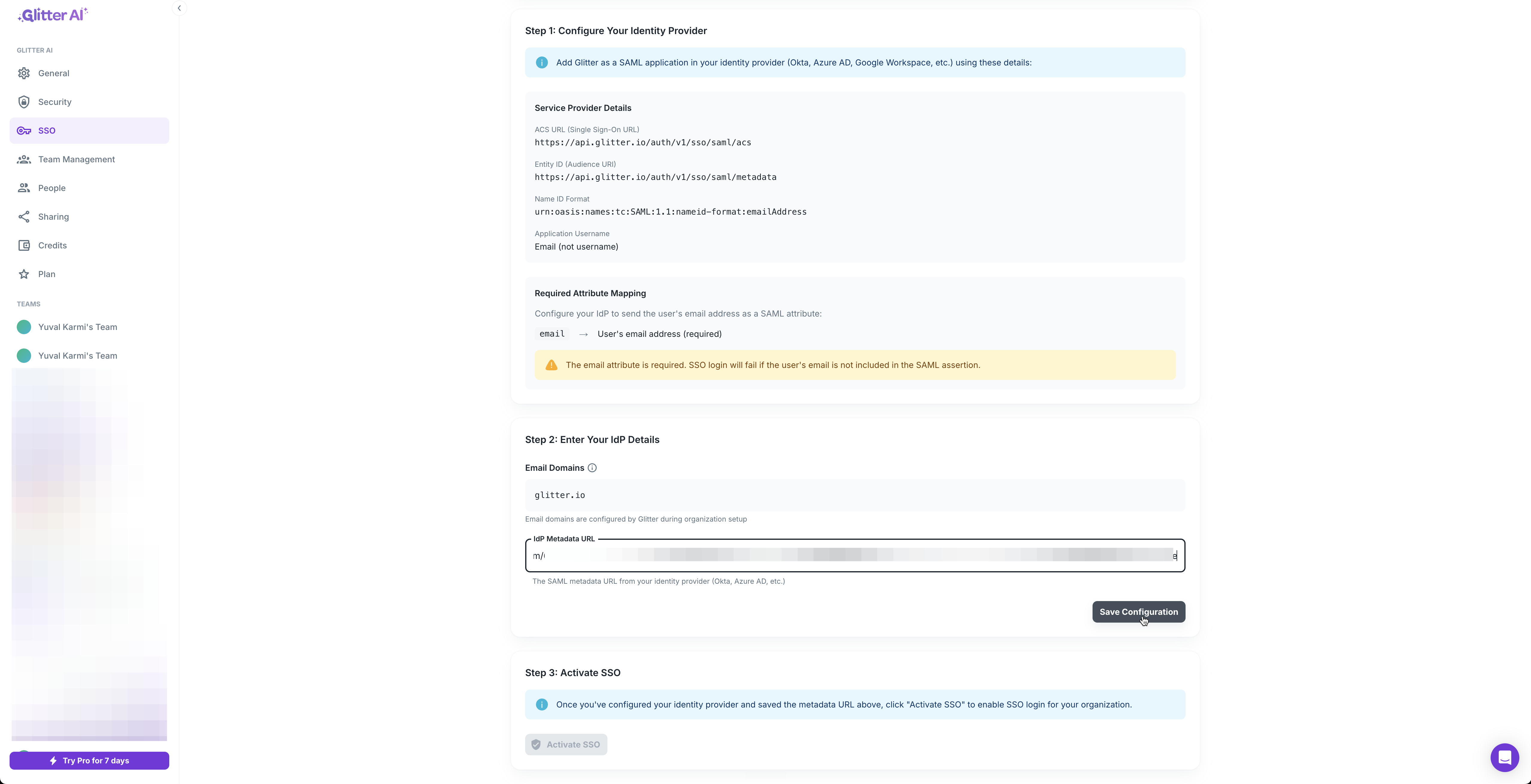
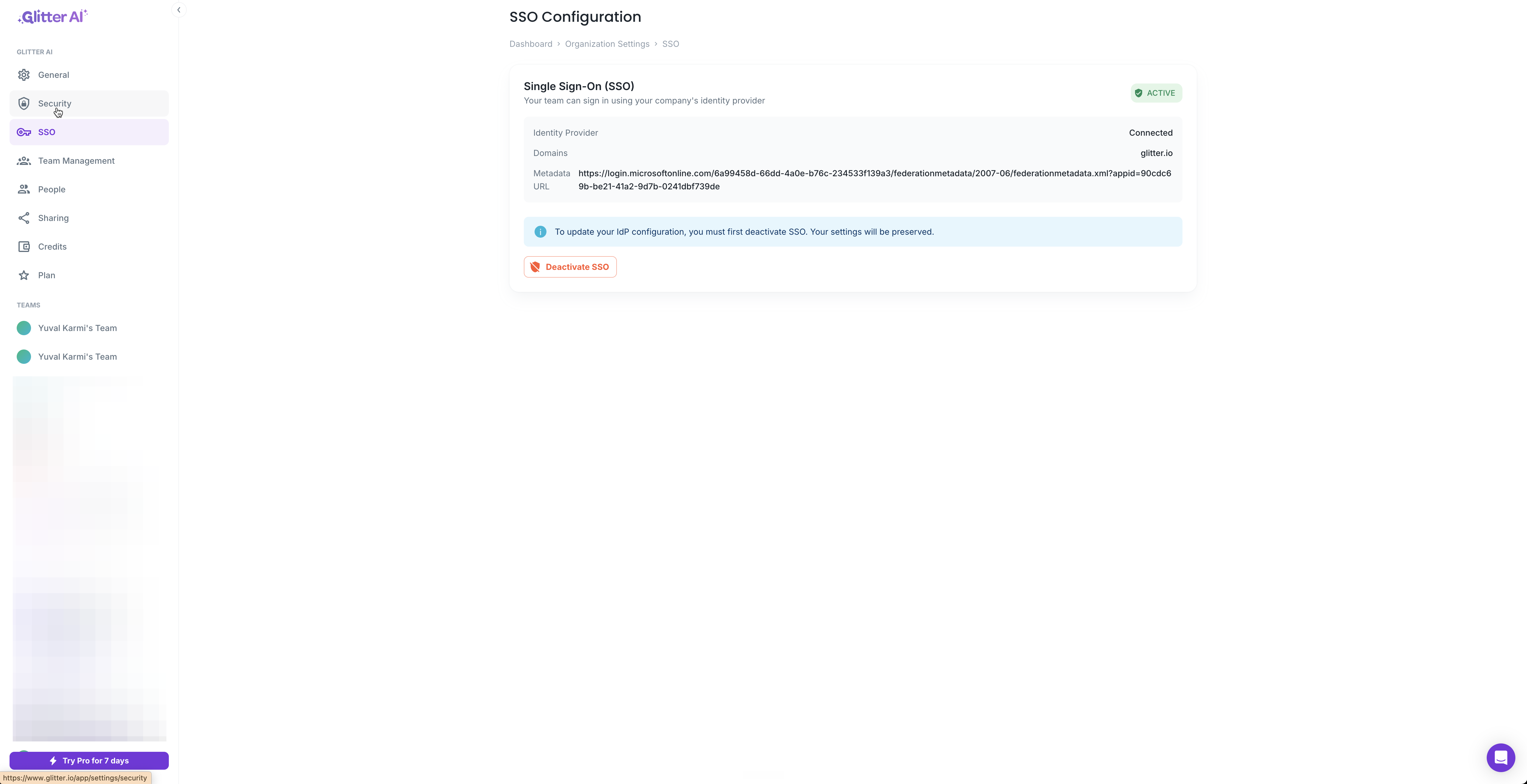
Finalize Configuration in Glitter AI
With Entra ID ready, you must provide its connection details back to Glitter AI.
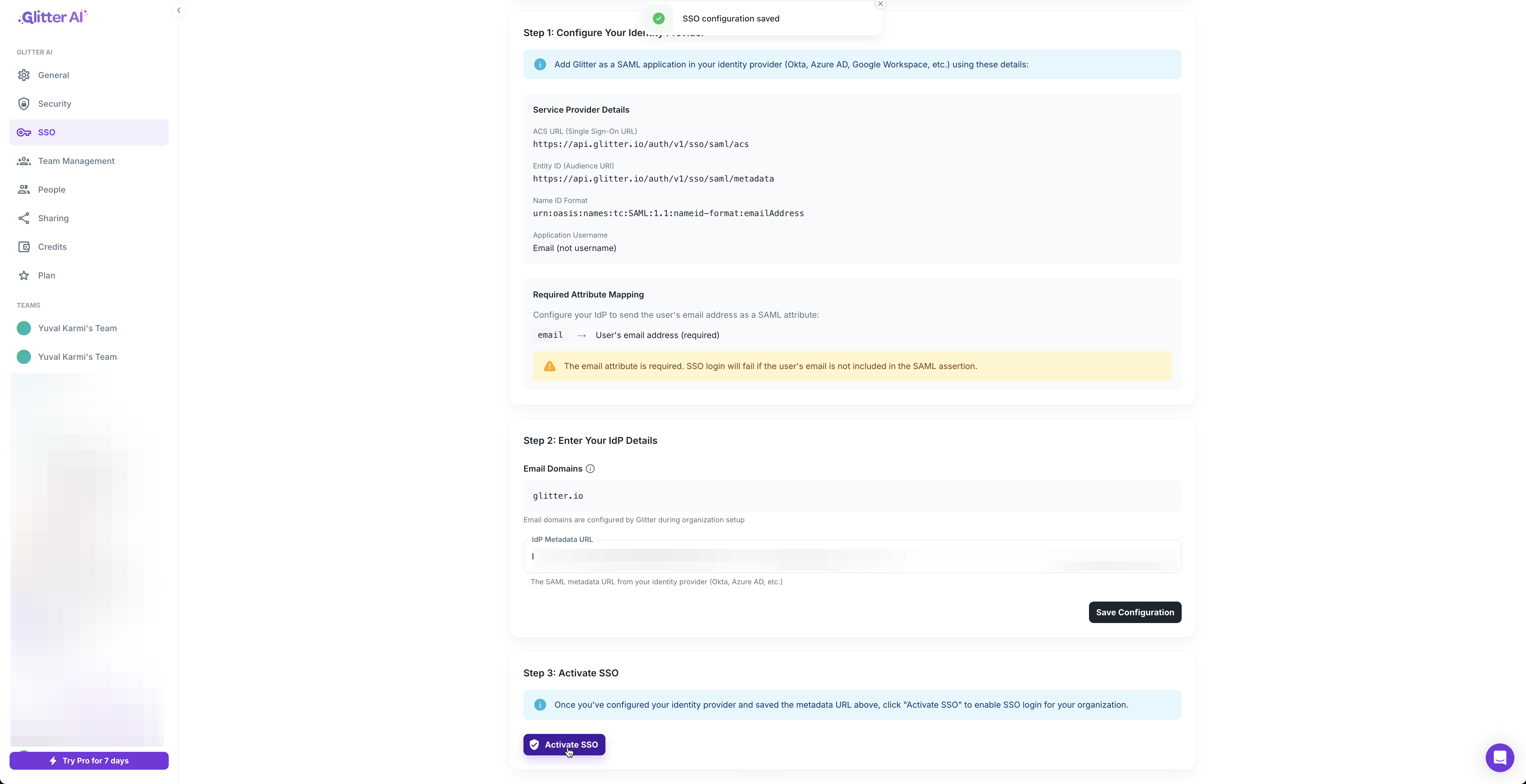
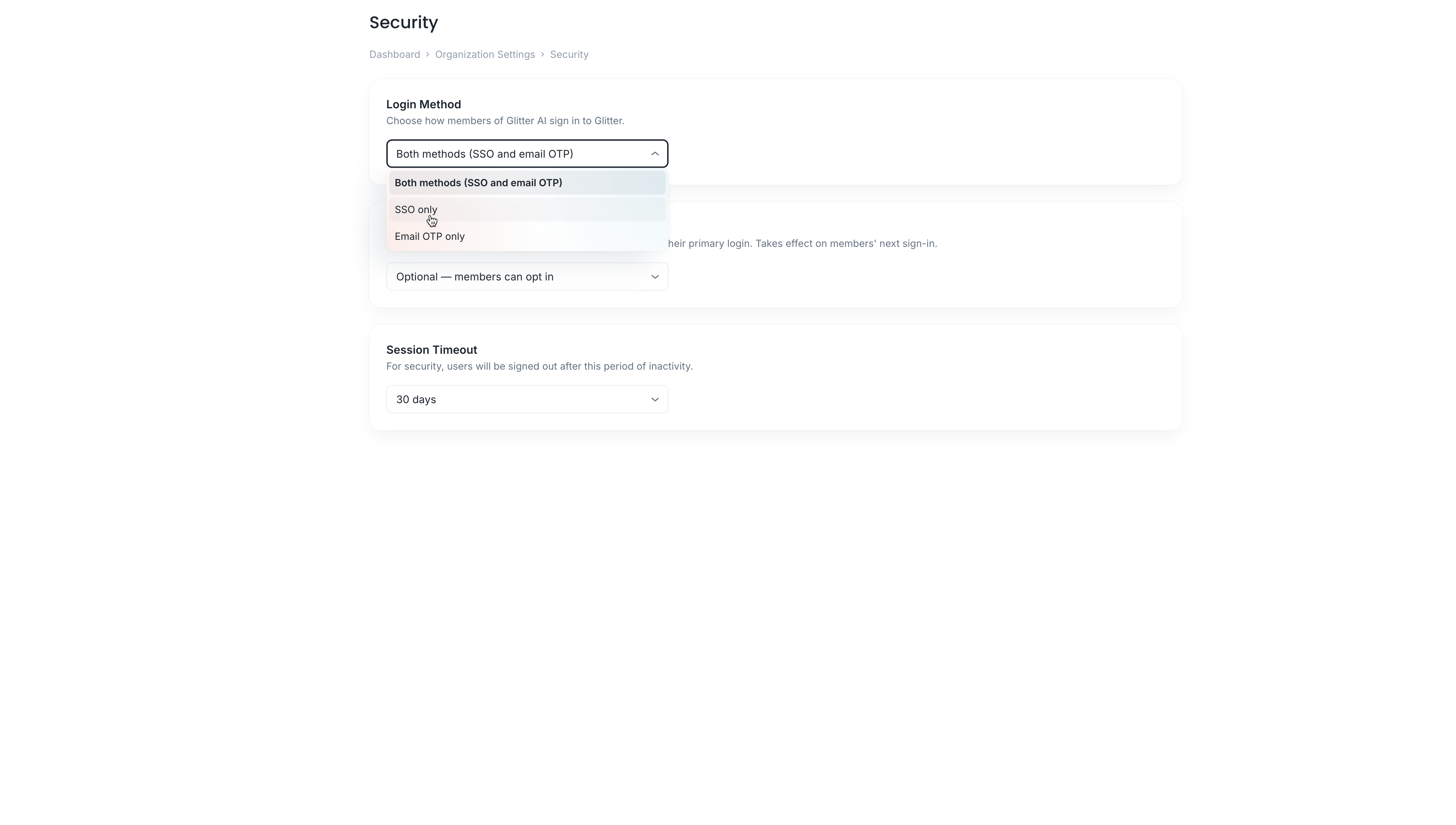
(Optional) Enforce SSO Only
By default, users can sign in using SSO or email OTP. You can enforce strict SSO routing to mandate that users authenticate via Entra ID.
FAQ
Q: Why isn't SSO authentication working for my users?
A: The most common cause is a mismatch in attributes. Ensure the "Unique User Identifier" in Entra ID's Attributes & Claims settings properly maps to user.userprincipalname and is formatted to pass the user's email address.
Q: Can I use both SSO and Email OTP login options simultaneously?
A: Yes. Under Glitter AI's Security tab, you can set the Login Method to "Both methods" to support a mixed authentication approach.
Glossary
Term | Definition |
|---|---|
ACS URL | Assertion Consumer Service URL. The destination where the Identity Provider (Entra ID) sends its SAML authentication response. |
Identity Provider (IdP) | A system entity that creates, maintains, and manages identity information while providing authentication services (e.g., Microsoft Entra ID). |
SAML | Security Assertion Markup Language. An open standard that allows identity providers to pass authorization credentials to service providers. |